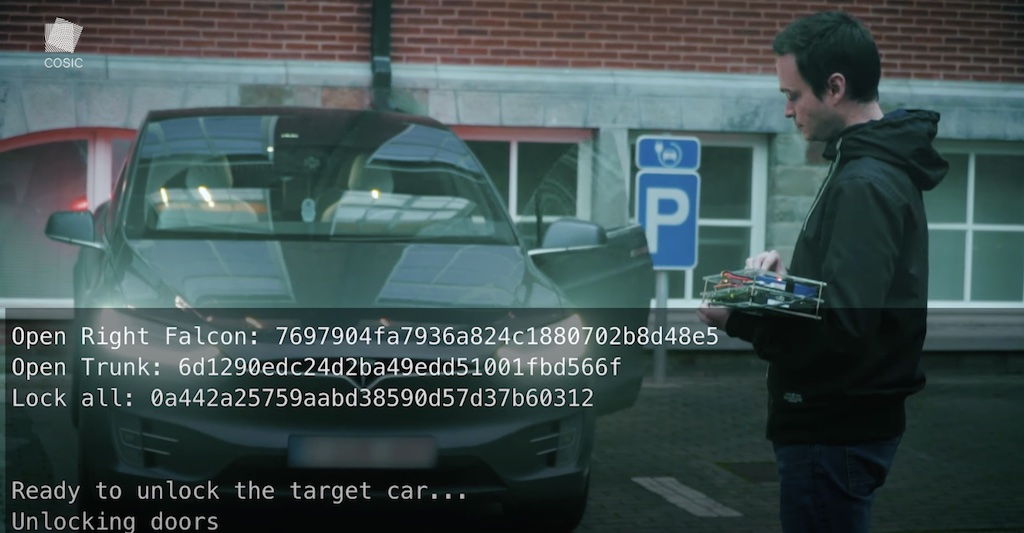
A new attack has been announced from Belgium that allows the cloning of the access ‘key’ of Elon Musk’s electric cars. The demonstration of this hack has been done with a Tesla Model X.
The system developed by the cryptographic security researcher at the KU Leven University in Belgium bases its hacking tool on exceeding the limits of cryptography that the Model X key fob has.
Lenner Wouters, a researcher author of the hack, explains in Wired how his system works to breach Tesla’s security.
“Basically, a combination of two vulnerabilities allows a hacker to steal a Model X in a few minutes.”
Wouters’ technique exploits a number of vulnerabilities in vehicle security in the Model X keyless entry module.
Together, these detected faults “form a method to unlock completely, start, and steal a vehicle.” clarifies the researcher.
The first part of the attack on the Californian electric car works as follows:
“First, Model X key fobs lack what is known as “code signing” for their firmware updates. Tesla designed its Model X key fobs to receive over-the-air firmware updates via Bluetooth by connecting wirelessly to the computer inside a Model X, but without confirming that the new firmware code has an unforgeable cryptographic signature from Tesla. “
The Belgian researcher has been able to turn his computer into a Bluetooth radio to connect to the key fob of the Model X used in the demonstration.
From this moment on, it could remake the firmware and consult the existing secure key chip inside the ‘key ring,’ accessing the generated unlock code.
With this information, he could transfer the data to his computer via Bluetooth, achieving full access to the electric car. The entire process only took 90 seconds.
Tesla has been notified of the security hole, and, according to the Electreck portal, it will launch a patch to its fleet of vehicles to correct this deficiency.
The California firm pays close attention to ‘white hat’ hackers. Over the last few years, it has organized competitions with economic prizes so that these cybersecurity specialists find violations in their cars.